How Application Load Balancers Improve User Experience
May 7, 2026In today’s digital world, users expect applications and websites to load instantly, remain available 24/7, and deliver a seamless experience without interruptions. Whether it’s an e-commerce platform, banking application, government portal, or enterprise software, performance and reliability directly impact customer...
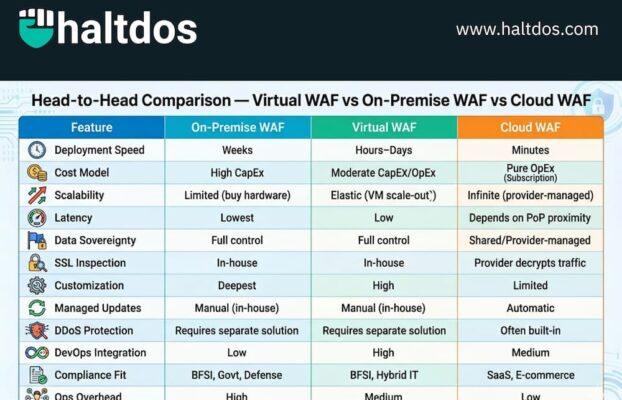
Virtual WAF vs On-Premise WAF vs Cloud WAF: Which Is Best for You? (2026 Guide)
April 20, 2026A Web Application Firewall (WAF) is no longer optional — it’s a foundational layer of any serious application security strategy. But choosing how to deploy one is where most organizations get stuck. Should you buy a physical appliance and run...
How to Secure Your Infrastructure from Next-Gen Bot Attacks – And How Haltdos (Make in India) Is Leading the Cyber War
April 3, 2026Introduction: The Bot is Not What It Used to Be Remember when bot attacks were just simple scripts trying to stuff login credentials? Those days are over. Today, we face Fifth-Generation Bots—AI-driven, polymorphic, and disturbingly human-like. These new-generation bots can: For...
Anycast vs. Scrubbing Center Architecture: What DDoS Mitigation Vendors Won’t Tell You About Latency Trade-offs Under Sustained Attack
March 13, 2026The two dominant paradigms for volumetric DDoS mitigation — Anycast-based scrubbing and on-demand traffic diversion to dedicated scrubbing centers — represent fundamentally different trade-offs between baseline latency, mitigation capacity, detection lag, and operational complexity. Understanding which trade-offs your infrastructure can...
DNS Firewall: The Overlooked Layer in Cyber Defense
March 3, 2026According to the latest Verizon Data Breach Investigations Report (DBIR), over 90% of malware uses DNS at some stage of the attack lifecycle—whether for command-and-control (C2), data exfiltration, or lateral movement. Yet, DNS security remains one of the most overlooked...
Securing the “Swadeshi” AI Stack: Indigenous Models need Indigenous Security
February 23, 2026India’s push for sovereign AI has gained unprecedented global spotlight following the India AI Impact Summit 2026, a landmark event held from February 16–20 at Bharat Mandapam in New Delhi. Inaugurated by Prime Minister Narendra Modi, this first-ever major AI...
OWASP Model Explained: Why Developers Must Know OWASP for Secure Coding
January 16, 2026Introduction: Why Application Security Matters Today Modern cyberattacks rarely start at the network layer. Instead, attackers target web applications, APIs, and business logic. Poor input validation, weak authentication, or insecure design can expose sensitive data within minutes. This is why...
Cloud WAF vs On-Premise WAF: Which Web Application Firewall Is Right for Your Business?
January 13, 2026With the rapid rise in web-based attacks such as SQL injection, cross-site scripting (XSS), and DDoS, securing web applications has become a top priority for businesses. A Web Application Firewall (WAF) plays a critical role in protecting applications by filtering...
The Rise of AI-Powered Cyber Attacks: Why Your Business Needs Next-Generation Defense
December 10, 2025The cybersecurity landscape has fundamentally transformed. Modern cyberattacks are no longer crafted by human hackers alone—they’re orchestrated by artificial intelligence systems that learn, adapt, and strike with unprecedented speed and sophistication.As we navigate through 2025, enterprises face a critical inflection...